Malware analysis Malicious activity
$ 24.50
In stock
Product Description

Security Orchestration Use Case: Automating Malware Analysis
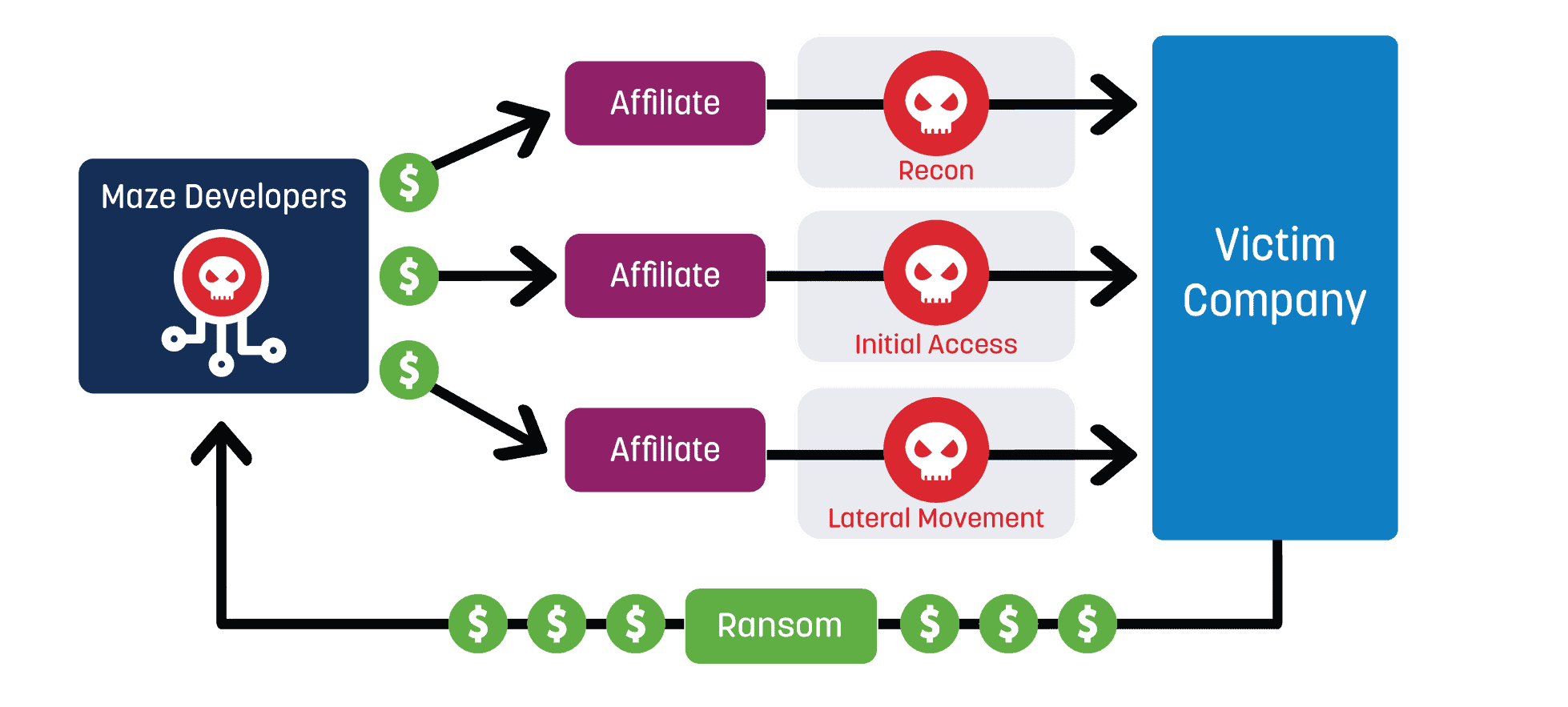
Top Ransomware Detection Techniques
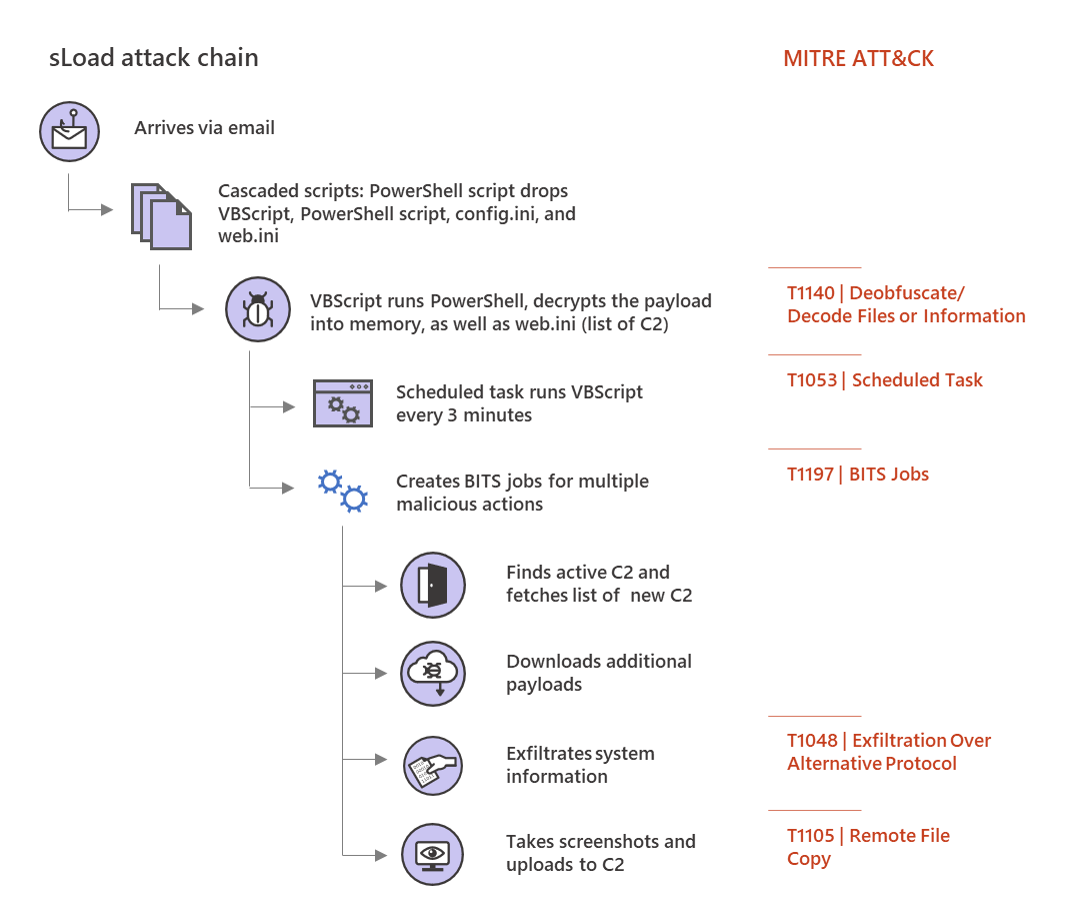
Multi-stage downloader Trojan sLoad abuses BITS almost exclusively
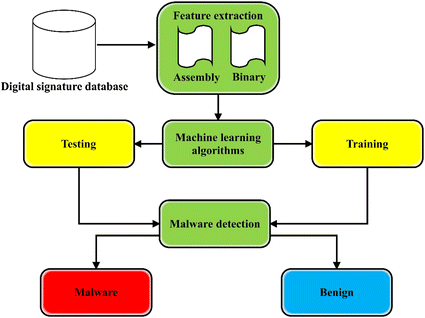
A state-of-the-art survey of malware detection approaches using
Malware Analysis: Static vs. Dynamic and 4 Critical Best Practices
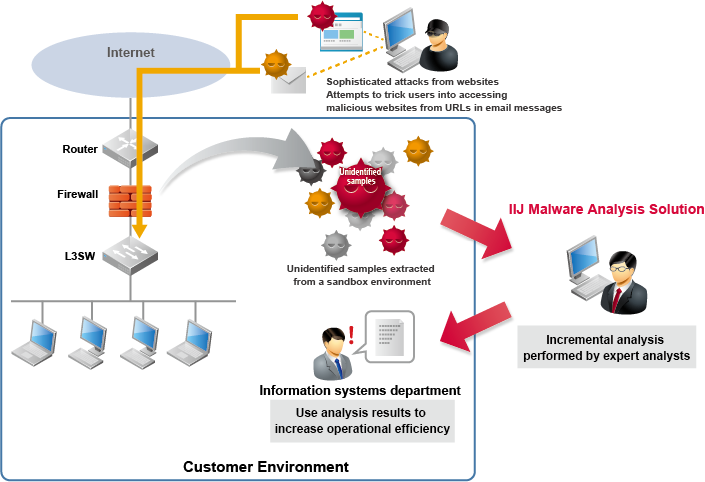
IIJ Malware Analysis Solution, Business
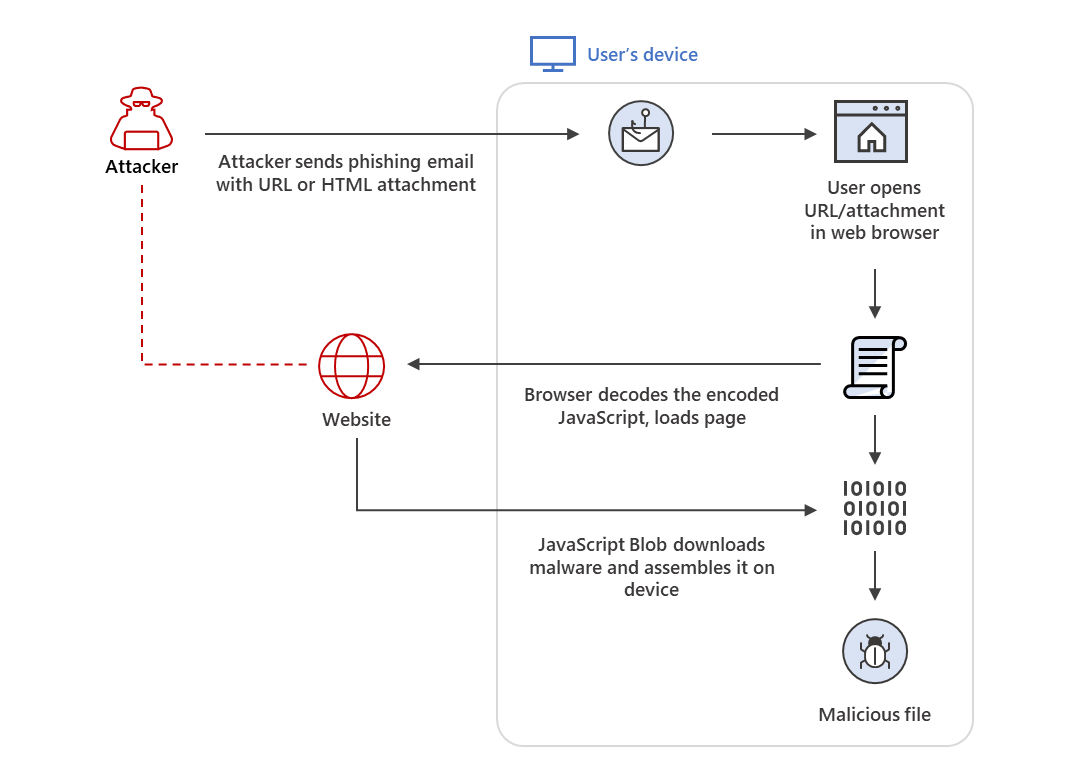
HTML smuggling surges: Highly evasive loader technique

Dynamic malware analysis flowchart

MALWARE DETECTION : EVASION TECHNIQUES - CYFIRMA
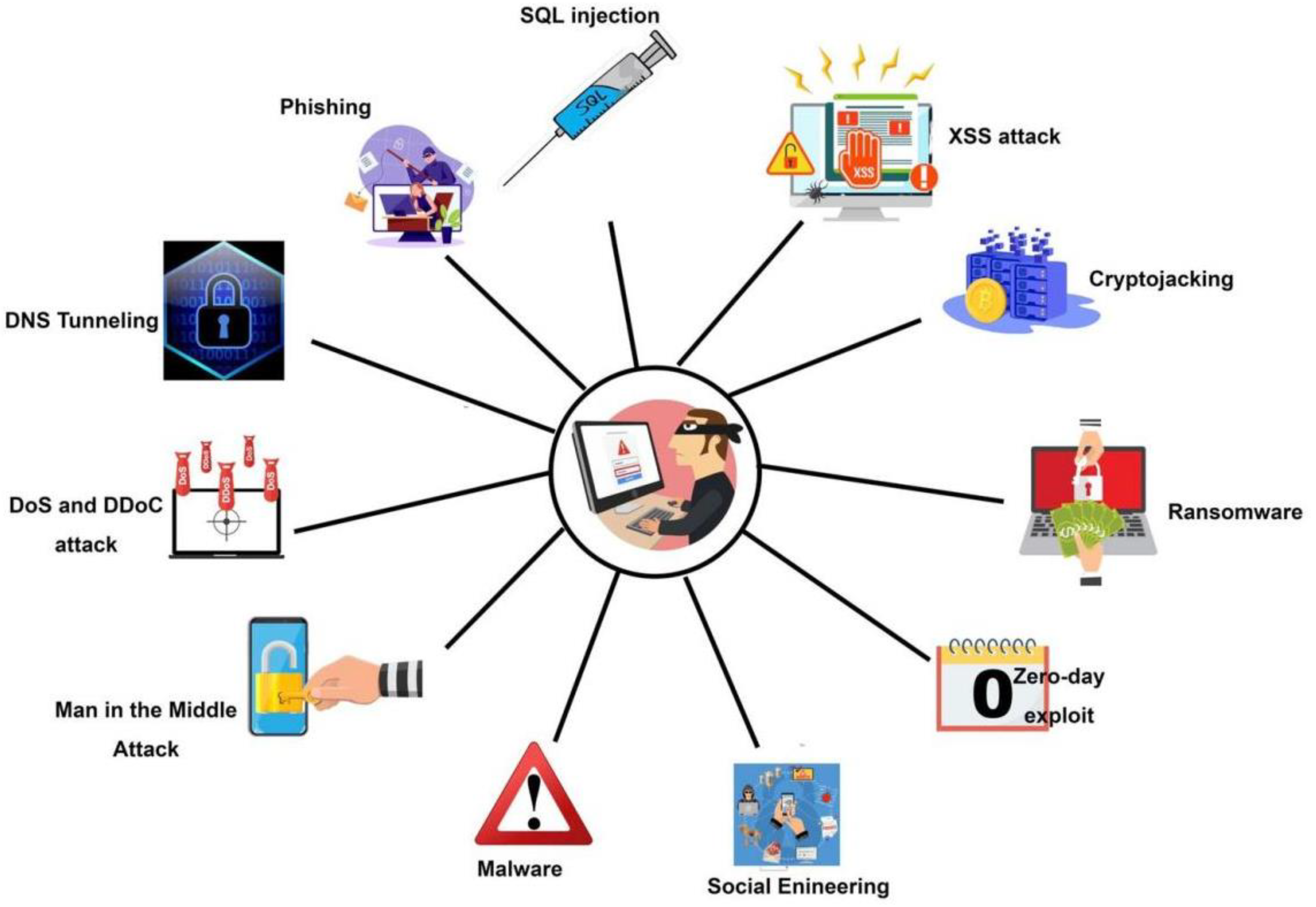
Symmetry, Free Full-Text





/cdn.vox-cdn.com/uploads/chorus_image/image/60819877/592244968.jpg.0.jpg)


