Malware analysis Malicious activity
$ 28.99
In stock
Product Description

Advanced Malware Detection – Signatures vs. Behavior Analysis - Cyber Defense Magazine

Malware analysis: Hands-On Shellbot malware – Sysdig

Malware Analysis Solutions - Fast & Accurate Detection - OPSWAT

Malware Analysis — Part 1. Malware, as the name indicates is…, by Akash Sarode
11 Best Malware Analysis Tools and Their Features
Virtualization/Sandbox Evasion - How Attackers Avoid Malware Analysis

Security Orchestration Use Case: Automating Malware Analysis - Palo Alto Networks Blog
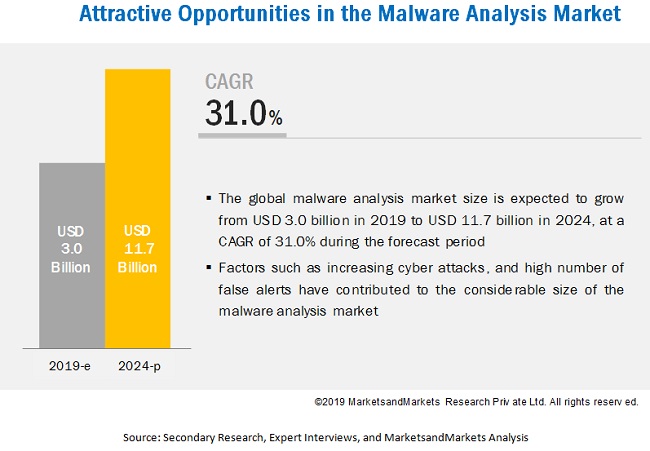
Malware Analysis Market Growth Drivers & Opportunities
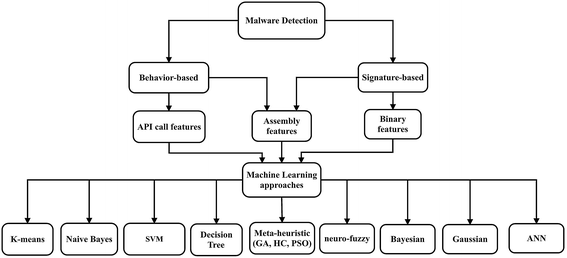
A state-of-the-art survey of malware detection approaches using data mining techniques, Human-centric Computing and Information Sciences
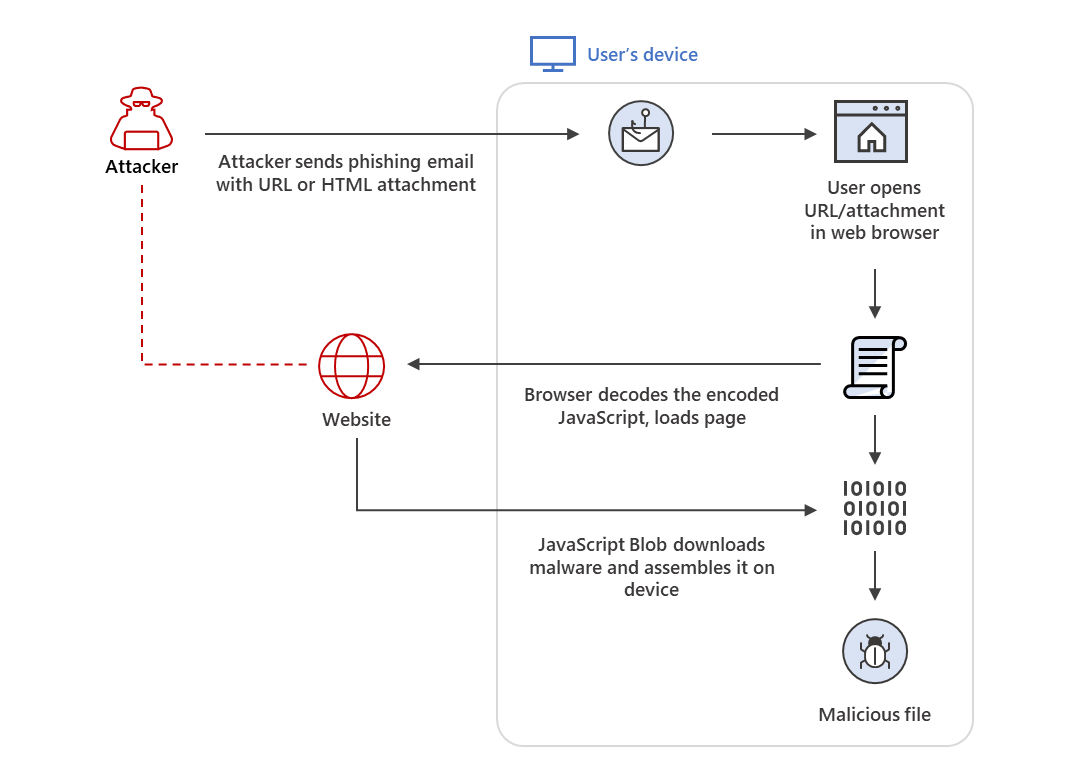
HTML smuggling surges: Highly evasive loader technique increasingly used in banking malware, targeted attacks

Behavior-based malware analysis process as conducted by our

Malware Analysis: Steps & Examples - CrowdStrike

Detail procedure of malware analysis
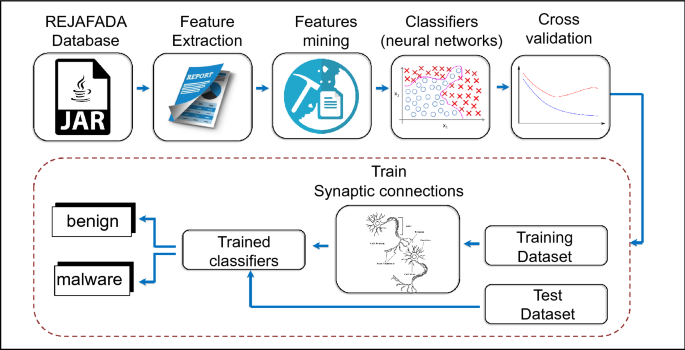
Antivirus applied to JAR malware detection based on runtime behaviors

VMRay Blog: Cyber Security & Malware Analysis Insights









